 |
|
Please Whitelist This Site?
I know everyone hates ads. But please understand that I am providing premium content for free that takes hundreds of hours of time to research and write. I don't want to go to a pay-only model like some sites, but when more and more people block ads, I end up working for free. And I have a family to support, just like you. :)
If you like The TCP/IP Guide, please consider the download version. It's priced very economically and you can read all of it in a convenient format without ads.
If you want to use this site for free, I'd be grateful if you could add the site to the whitelist for Adblock. To do so, just open the Adblock menu and select "Disable on tcpipguide.com". Or go to the Tools menu and select "Adblock Plus Preferences...". Then click "Add Filter..." at the bottom, and add this string: "@@||tcpipguide.com^$document". Then just click OK.
Thanks for your understanding!
Sincerely, Charles Kozierok
Author and Publisher, The TCP/IP Guide
|
|
|

Custom Search
|
|
IPSec Encapsulating Security Payload (ESP)
(Page 2 of 4)
Encapsulating Security Payload Operations and Field Use
Let's try to explain this procedurally, by considering three basic steps performed by ESP.
The first thing to consider is how the ESP header is placed; this is similar to how AH works:
- IPv6: The ESP Header is inserted
into the IP datagram as an extension header, following the
normal IPv6 rules for extension header linking.
In transport mode, it appears before a Destination Options header
containing options intended for the final destination, but after any
other extension headers, if present. In tunnel mode, it appears as an
extension header of the new IP datagram that encapsulates the original
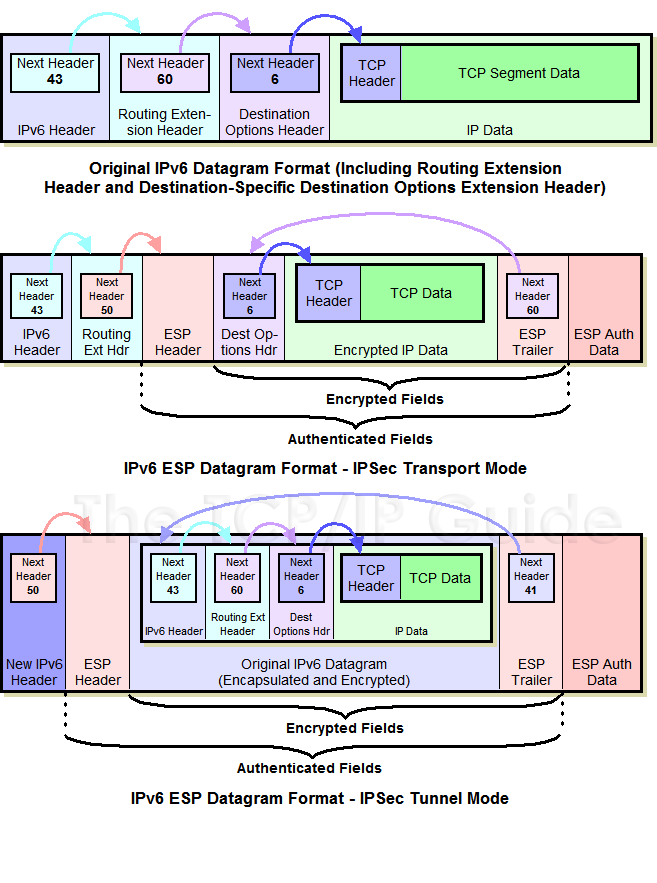
one being tunneled. This can be seen in Figure 124.
Figure 124: IPv6 Datagram Format With IPSec Encapsulating Security Payload (ESP)
At top is the same example IPv6 datagram with two extension headers shown in Figure 121. When ESP is applied in transport mode, the ESP Header is added to the existing datagram as in AH, and the ESP Trailer and ESP Authentication Data are placed at the end. In tunnel mode, the ESP Header and Trailer bracket the entire encapsulated IPv6 datagram. Note the encryption and authentication coverage in each case, and also how the Next Header field “points back” into the datagram since it appears in the ESP Trailer.
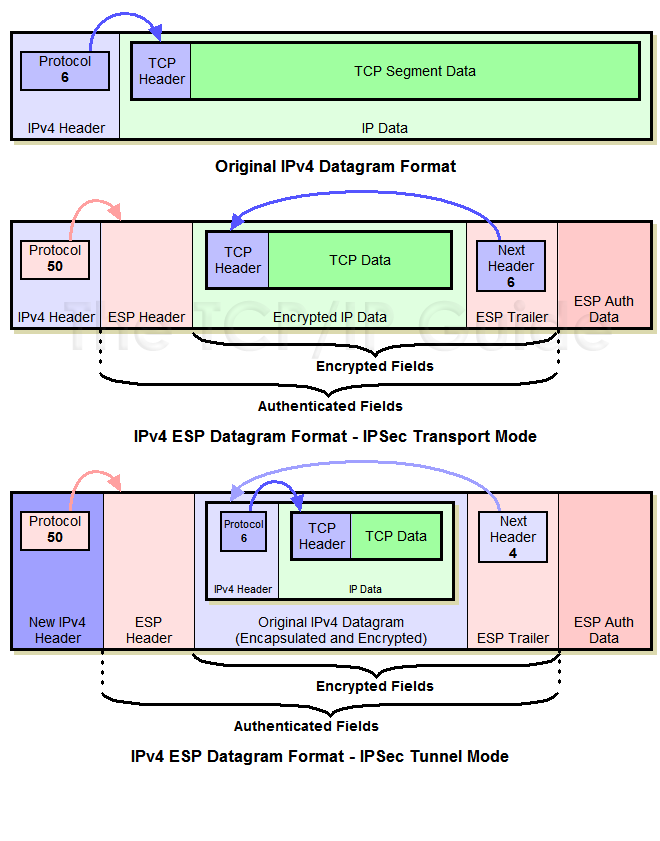
- IPv4: As with the AH, the ESP
Header is placed after the normal IPv4 header. In transport mode,
it appears after the original IP header; in tunnel mode, after the IP
header of the new datagram encapsulating the original. This is shown
in Figure 125.
Figure 125: IPv4 Datagram Format With IPSec Encapsulating Security Payload (ESP)
At top is the same sample IPv4 datagram shown in Figure 122. When this datagram is processed by ESP in transport mode, the ESP Header is placed between the IPv4 header and data, with the ESP Trailer and ESP Authentication Data following. In tunnel mode, the entire original IPv4 datagram is surrounded by these ESP components, rather than just the IPv4 data. Again, as in Figure 124, note the encryption and authentication coverage, and how the Next Header field “points back” to specify the identity of the encrypted data/datagram.
|
| |||||||||||||||||||
Home - Table Of Contents - Contact Us
The TCP/IP Guide (http://www.TCPIPGuide.com)
Version 3.0 - Version Date: September 20, 2005
© Copyright 2001-2005 Charles M. Kozierok. All Rights Reserved.
Not responsible for any loss resulting from the use of this site.






