 |
|
Please Whitelist This Site?
I know everyone hates ads. But please understand that I am providing premium content for free that takes hundreds of hours of time to research and write. I don't want to go to a pay-only model like some sites, but when more and more people block ads, I end up working for free. And I have a family to support, just like you. :)
If you like The TCP/IP Guide, please consider the download version. It's priced very economically and you can read all of it in a convenient format without ads.
If you want to use this site for free, I'd be grateful if you could add the site to the whitelist for Adblock. To do so, just open the Adblock menu and select "Disable on tcpipguide.com". Or go to the Tools menu and select "Adblock Plus Preferences...". Then click "Add Filter..." at the bottom, and add this string: "@@||tcpipguide.com^$document". Then just click OK.
Thanks for your understanding!
Sincerely, Charles Kozierok
Author and Publisher, The TCP/IP Guide
|
|
|

Custom Search
|
IPSec Authentication Header (AH)
(Page 3 of 4)
IPv4 Authentication Header Placement and Linking
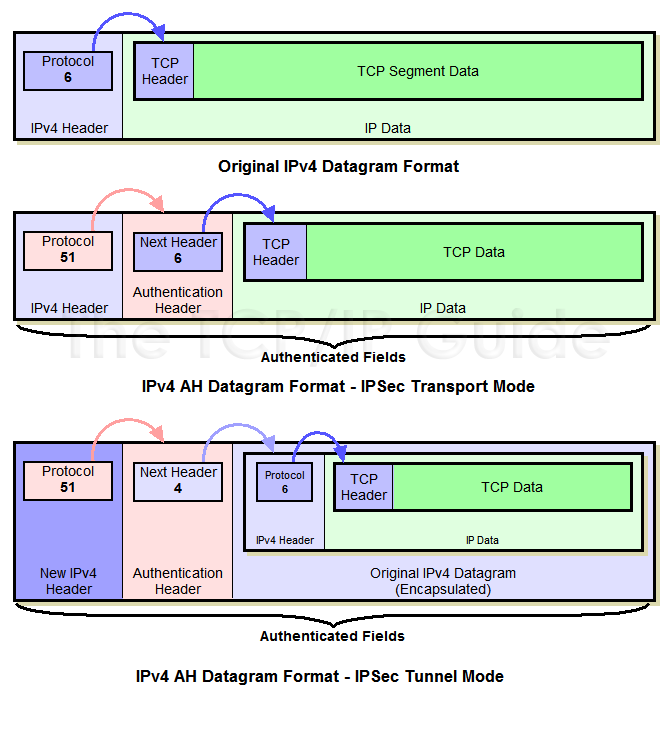
A method that is similar to the IPv6 header linking technique is employed. In an IPv4 datagram, the Protocol field indicates the identity of the higher layer protocol (typically TCP or UDP) carried in the datagram. As such, this field “points” to the next header, which is at the front of the IP payload. AH takes this value and puts it into its Next Header field, and then places the protocol value for AH itself (51 decimal) into the IP Protocol field. This makes the IP header “point” to the AH, which then “points” to whatever the IP datagram pointed to before.
Again, in transport mode, the authentication header is added after the main IP header of the original datagram; in tunnel mode it is added after the new IP header that encapsulates the original datagram being tunneled. This is shown in Figure 122.
|
|
|
| |||||||||||||||||||
Home - Table Of Contents - Contact Us
The TCP/IP Guide (http://www.TCPIPGuide.com)
Version 3.0 - Version Date: September 20, 2005
© Copyright 2001-2005 Charles M. Kozierok. All Rights Reserved.
Not responsible for any loss resulting from the use of this site.







 Key Concept: The IPSec Authentication Header (AH) protocol allows the recipient of a datagram to verify its authenticity. It is implemented as a header added to an IP datagram that contains an integrity check value computed based on the values of the fields in the datagram. This value can be used by the recipient to ensure that the data has not been changed in transit. The Authentication Header does not encrypt data and thus does not ensure the privacy of transmissions.
Key Concept: The IPSec Authentication Header (AH) protocol allows the recipient of a datagram to verify its authenticity. It is implemented as a header added to an IP datagram that contains an integrity check value computed based on the values of the fields in the datagram. This value can be used by the recipient to ensure that the data has not been changed in transit. The Authentication Header does not encrypt data and thus does not ensure the privacy of transmissions.